Integrating AppSweep and GitHub to Automate Your Mobile App Security Testing

Why integrate with GitHub?
Integrating AppSweep, Guardsquare’s mobile application security testing tool, with GitHub allows developers to automatically analyze their mobile app for potential security issues. AppSweep can detect potential issues like insecure communication, poor cryptography, and more.
By automating your mobile testing process, security testing is automatically triggered from within your Continuous Integration pipeline, and your team can quickly see links to your scan results directly attached to a pull request. This ensures you have instant, actionable feedback to improve the security posture of your mobile application.
How to set up the AppSweep GitHub Integration
In order to integrate with GitHub three things need to be set up:
- The AppSweep Gradle plugin needs to be used to build your app. This ensures apps are automatically uploaded for scanning.
- The AppSweep GitHub App needs to be installed on your GitHub account, which enables automated triggering of the app scan.
- The AppSweep App will need GitHub repository access enabled for AppSweep to post the results summary back.
Setting up the AppSweep Gradle plugin
Our AppSweep plugin is published in the Gradle Public Repository, and can be easily added to your Android project by adding the following to yourapp/build.gradle:
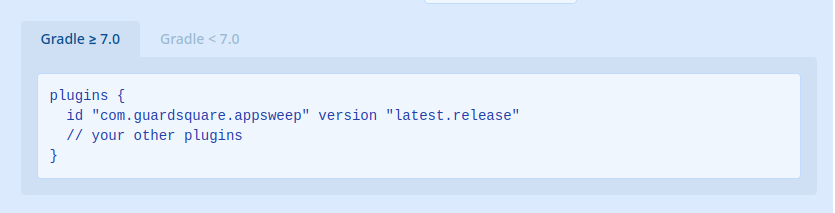
Note: the dynamic versionlatest.releaserequires at least Gradle 7. If you want to build with an older Gradle version, you need to specify a version number. The latest version number can be found in the Gradle Plugins Portal.
Next, you need to configure the plugin by providing an API key for your project. You can create an API key in the API Keys section of your project settings on the AppSweep website.
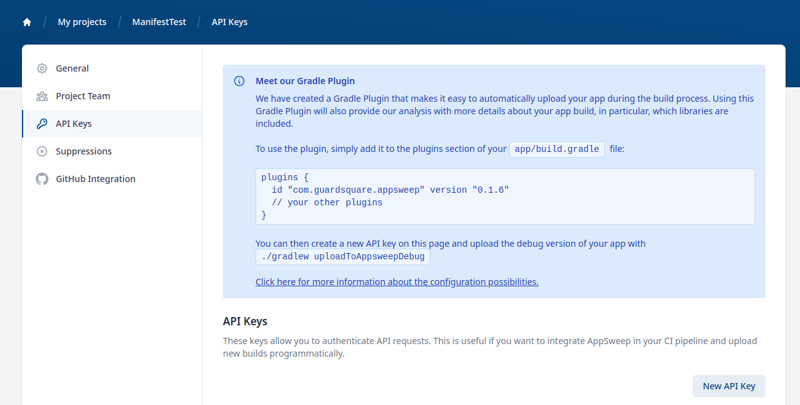
The key can be easily tested locally with:
APPSWEEP_API_KEY=gs_appsweep_SOME_API_KEY ./gradlew uploadToAppSweepDebugAppSweep uses commit hashes in order to associate pull requests on GitHub to app scans. By using our AppSweep Gradle plugin, the commit hashes are automatically attached to the scan.
There are more advanced configuration options for the Gradle plugin which are explained on https://github.com/Guardsquare/appsweep-gradle.
Automating the scanning process with a GitHub action workflow
In order to automate the process, it is possible to use a simple GitHub action. The following action will trigger the AppSweep scan on each pull request to the branch with the workflow.
.github/workflows/github-action-appsweep.yml
name: AppSweep mobile application security testing
on: [pull_request_target]
jobs:
upload-app-to-appsweep:
runs-on: ubuntu-latest
steps:
- name: Check out repository code
uses: actions/checkout@v2
- name: Upload app to AppSweep with Gradle
env:
APPSWEEP_API_KEY: $
run: ./gradlew uploadToAppSweepRelease
APPSWEEP_API_KEYwhich will be picked up by the Gradle plugin.
Reminder: The presented GitHub action is using the pull_request_target event which will be triggered if anyone creates a push request to the branch. For example, the presented workflow can be stored on the master; then, if someone makes a pull request, the workflow will be triggered. The pull_request_target event allows for GitHub secret access, which allows it to securely store API keys.
Install the AppSweep App on your GitHub account
Installing AppSweep on your GitHub account allows AppSweep to report the results back to GitHub, and attach them to the pull request. Installing it is very easy.
Simply follow this link: https://appsweep.guardsquare.com/settings/integrations/github
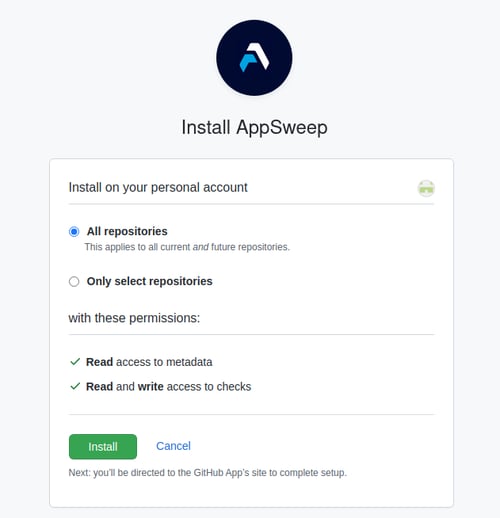
After clicking the installation link, you will be redirected to the installation process inside GitHub. If you belong to any organization then you will be asked if you would like to install AppSweep on your personal account or for organization use.
You will be asked to choose which GitHub repositories you would like to use AppSweep for. This permission allows AppSweep to access the chosen repositories (you will be asked to select one of the chosen repositories in the next step).
After that just press the Install button.
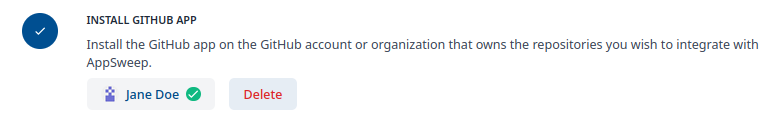
On the GitHub integration page inside AppSweep, you can then verify the successful installation of the GitHub app. You should see a green checkmark next to your GitHub login:
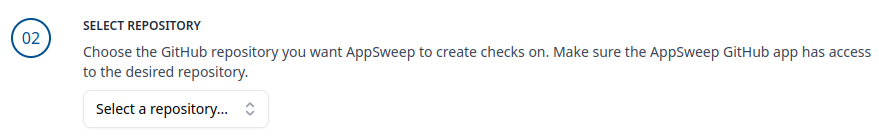
Now you can choose a repository to link with AppSweep. This list contains the set of all previously selected repositories.
After selecting the repository a green checkmark will be visible next to its name, indicating that the GitHub App was successfully installed for this repository.
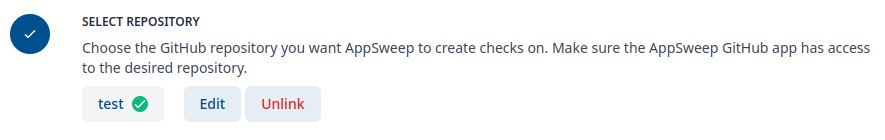
The integration with Github is complete. AppSweep is now able to post scan results back to GitHub.
To fully automate this, you will now need to set up the Gradle plugin.
Viewing AppSweep scan results in GitHub
After configuring the AppSweep Gradle plugin, the GitHub action workflow, and the GitHub App, the results of a scan are posted directly to your GitHub repository. After creating a pull request, the action will schedule a scan of your application. Typically after a few minutes, the scan will be finished and the results of the scan will be visible in the pull request.
! It is essential that the pull request is created before the Gradle AppSweep task is executed. Otherwise, the result will not be attached to the pull request. !
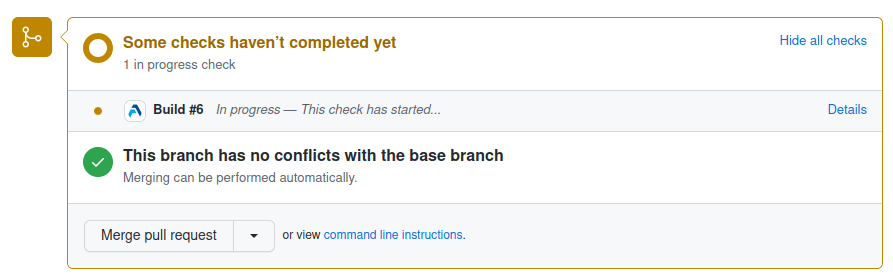
Immediately after the action triggers the Gradle task, you will see notifications that the checks are running:
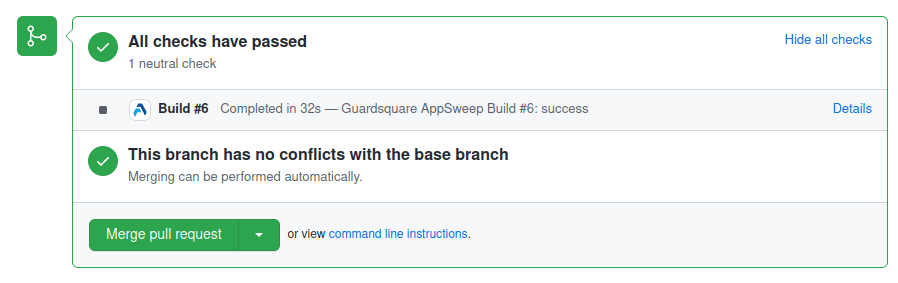
Once it is finished, the display on GitHub is updated:
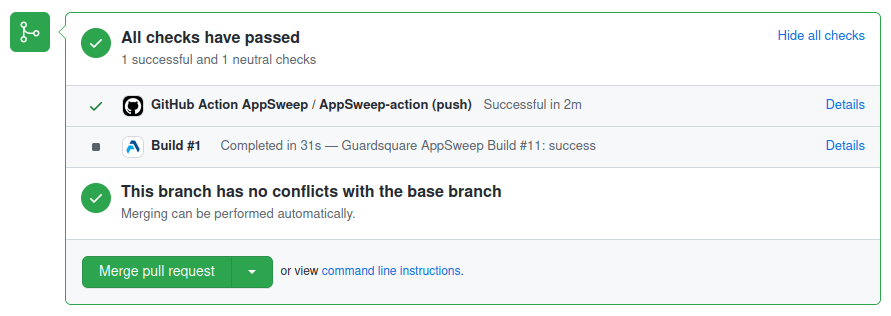
Entering the Details, you can see the details of the scan and a summary describing the detected issues in the Checks section.
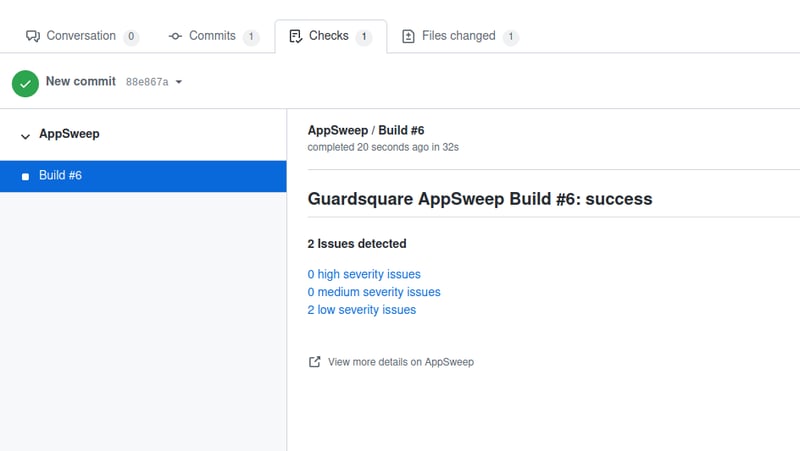
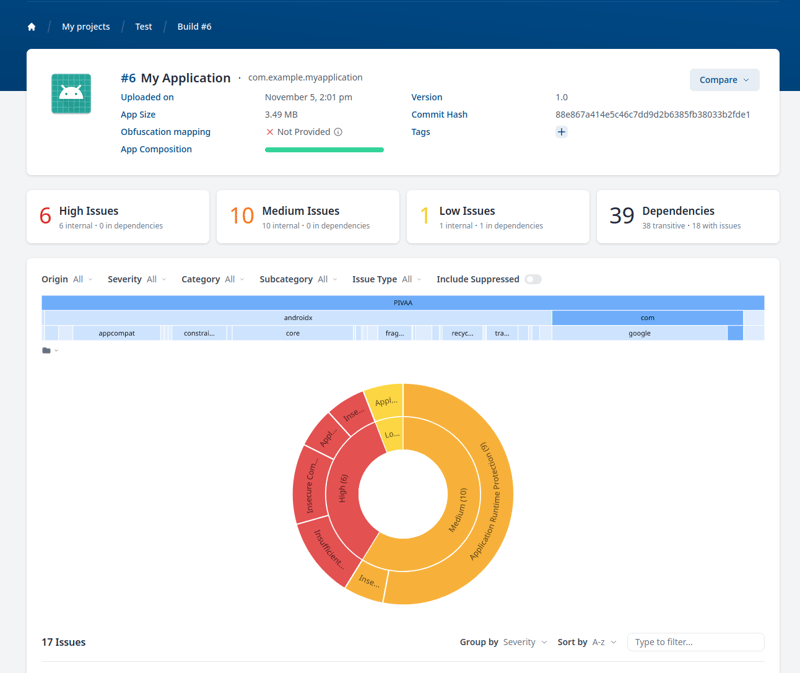
To see the detailed findings for your scan, you can go directly to AppSweep by clicking View more details on AppSweep:
Reminder: The AppSweep GitHub App uses the commit hash to identify which commit the results should be attached to. Therefore, it is required to push this commit to GitHub before the analysis is finished. If the commit is not pushed yet, the results can still be viewed inside AppSweep.
Release your app with confidence
After completing these steps, you are now able to integrate AppSweep with GitHub, allowing you to access the results of an AppSweep scan on GitHub. By using the GitHub action, the workflow can be fully automated, and can be triggered during each pull request.
Implementing this automated workflow will help you identify new risks in your app even before they are merged into the main codebase, ensuring you identify security risks early in the development process. By following the actionable recommendations AppSweep provides to fix the issues, you can quickly address potential security risks and release your app with confidence.





