Mobile App Security Testing for Developers: It's Easier than You Think
According to a recent survey by Secure Code Warriors, only 14% of app developers consider security as a top priority while application performance and code quality rank at the top of the list. Interestingly, more than half of the interviewed developers expect security to become more important, despite the sentiment that security might be difficult or become a burden for them.
In a panel conversation featuring experienced mobile app developers, Dinorah Tovar Duarte - Google Developer Expert on Android, Arkham Finance, and Ubiratan Soares - Staff Software Engineer, Platform Engineering, N26 and Guardsquare’s Dennis Titze - AppSweep co-founder and development team lead discussed how mobile application security testing (MAST) can easily and effectively be integrated into development processes for apps across industries.
In particular, the panelists discussed four key MAST topics by sharing their hands-on experience.
What is MAST and how is it different from pentesting?
As Dinorah explained, “pentesting stands for penetration testing” and it is focused on finding specific vulnerabilities inside software applications or systems. It typically requires ”a very knowledgeable human being in security”, often a team of security experts. Usually pentesting is outsourced by the software developer company and seeks to find a particular weakness or risk. Pentesting is usually done before releasing an app and is often required for compliance with security standards in regulated markets, like financial services.
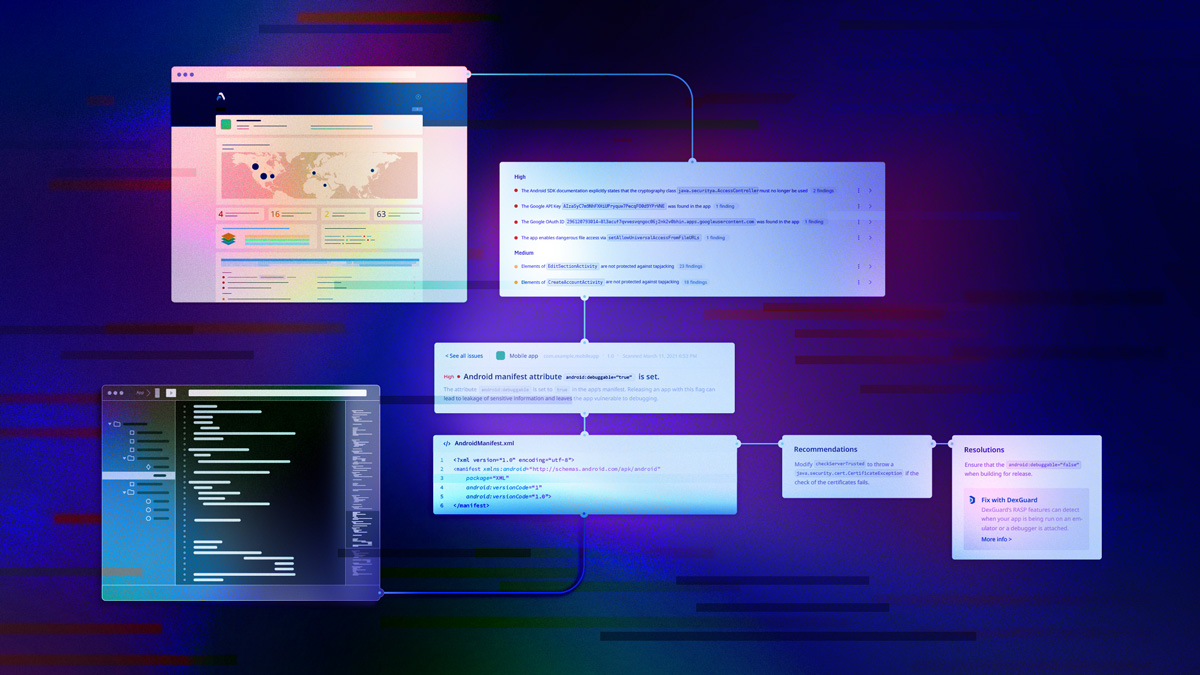
MAST, however, involves a series of techniques and tools that are often automated and help developers discover potential vulnerabilities on a broader scale. “MAST is actually something that you can put in place in your development process that can be easily automated,” Dinorah explained. “You don't need a security expert” because “usually [the tool] can be used by all mobile engineers on your team.” Because of these synergistic differences, MAST is complementary to pentesting. “You need to have both,” according to Dinorah, since “you want to be ready to solve a mistake [identified via MAST] before it becomes a really big monster that is gonna come and attack you”.
My apps are not in regulated markets, do I need MAST?
Adopting mobile app security in the financial sector, as Ubiratan's experience highlights, is crucial to satisfying the needs of all stakeholders, including auditors responsible for verifying compliance with standards mandated by regulators and major financial institutions. This may lead developers to assume mobile application security testing is optional for apps in sectors with less stringent regulatory requirements.
However, security measures “are meant to protect customers…from their own mistakes” like installing apps from unknown sources and exposing customers to potential malware. “[Security measures] also protect against [developers'] mistakes" such as insecure implementation of app functions like cryptography or network communication. To ensure apps are protected from both user and developer mistakes, mobile app security is beneficial across both regulated and unregulated industries.
“We can pick some examples in non-regulated markets”, Ubiratan noted. Consider, for instance, mobile games. An insecure communication between a mobile game and a server could be exploited by a threat actor to alter the gaming experience. While in a digital media app, by using MAST, developers could catch the incorrect implementation of cryptography used to protect content from piracy.
This example underscores the importance of embracing a "shift-left" approach and integrating MAST into every app development process regardless of market sector.
After all, as Ubiratan stated, "every customer deserves protection".
Are iOS apps more secure than Android apps?
Another common misconception is that the iOS platform is more secure than Android. As a result, iOS mobile app security is often deprioritized. According to Dennis, that shouldn’t be the case because “...in the end we see a lot of security issues in both android and iOS apps”.
As Dennis shared, “On both platforms mobile apps can have security flaws.“ In fact, “an application can have…arbitrary functionalities… [that lead to] arbitrary security flaws in your application”. Examples of this are incorrect cryptography or insecure communication implementation.
Additionally, he added, “Both Android and iOS provide some measures to protect applications from accessing other apps’ data.” But, at the same time, both platforms offer functionalities to share data between apps and other systems like back-end servers. If not implemented correctly, that could generate security issues. For example, an app leaking sensitive data like PII.
The security of the platform itself needs to be considered. Although iOS is perceived as a more secure environment, there are numerous examples of bypassing security measures on both platforms by rooting or jailbreaking the device.
The last point to consider is reverse engineering. On both platforms, without proper protections, it is possible for a threat actor to reverse the app to steal secrets or IP if it is not otherwise, and properly, protected.
“Long story short, iOS is not more secure than Android”, concluded Dennis.
MAST for non-security experts: Benefits for developers
Security is often deprioritized by developers who perceive it as an additional task detracting from their primary focus of developing mobile apps. As a result, they often prefer to leave it to security experts.
As Dinorah pointed out, having a security expert on the development team is definitely beneficial, but utilizing a MAST tool can effectively enhance the team's security expertise. "It provides metrics," she explained, enabling developers to assess their app's security posture on their own and assist team leaders in communicating security needs with stakeholders. With those metrics, Dinorah shared “you can easily reach out to your product manager, your scrum master, or other colleagues and discuss better how to allocate some time in Jira, in [your] Scrum sprint, to create more robust and secure software”. And if you use Github or similar platforms, Dinorah added, “it's quite simple to integrate [MAST] into your development pipeline as it is usually done with a script”. An additional recommendation shared by Dinorah about choosing the right MAST tool is “to make sure that the tool you are integrating is also based on a recognized [security] standard” making the metrics generated by the tool even more meaningful and actionable.
Ubiratan noted about mobile app security testing, “not only is it important, but it can also be fun”. “Engineers and developers shouldn’t be afraid of MAST”. It is an engaging learning experience for them, fostering a deeper understanding of how apps function. Moreover, extensive online resources, including openly shared mobile app security standards like OWASP MAS, provide valuable guidance for development teams.
Conclusion
With mobile apps becoming prime targets for threat actors across industries, it's crucial for developers to proactively discover and address vulnerabilities before they reach production, minimizing remediation costs, brand reputation impact and safeguarding user data.
MAST empowers developers to achieve this goal. Regardless of your experience in mobile app security, MAST’s ease of use, seamless integration, and actionable metrics ensure that security doesn’t slow down your development process.
MAST complements pentesting by identifying vulnerabilities earlier in the development cycle reducing cost and potential delays incurred when vulnerabilities are uncovered late in the development process.
Last but not least, no platform is immune to vulnerabilities. Although iOS is often perceived to be more secure than Android, both platform security measures can be bypassed by rooting or jailbreaking the devices, apps on those platforms can have similar weaknesses due to insecure implementations of app features or communication with other systems, and apps on both platforms can be easily reverse engineered.




