-
Products
-
Solutions
-
Resources
-
Company
- Pricing
Products
Solutions
Resources
Company

Mobile application protection involves techniques and tools used to defend mobile apps from tampering, reverse engineering, malware injection, and unauthorized access. Whether it's Android application protection or iOS app protection, the goal is to ensure the app's code, data, and functionality remain secure across environments.
Mobile device usage has grown rapidly, with smartphone usage projected to exceed 7 billion phones worldwide in 2024. As mobile continues to become the primary platform consumers use in their everyday lives, mobile app developers will need to prioritize security throughout the development lifecycle, both for Android and iOS mobile app protection.
Often, organizations prioritize time-to-market over in-app protection in their mobile app release cycles. However, once apps are downloaded, they escape the developer’s control. From there, malicious actors can disassemble or decompile apps using readily available tools, or they can focus on communications between the application and the organization’s server.
Android application protection focuses on defending against dynamic and static analysis, and mitigating platform-specific vulnerabilities. APK files can be easily extracted, decompiled, and analyzed by attackers, making Android apps especially vulnerable. Effective Android app protection includes code obfuscation, root and emulator detection, secure key management, and runtime application self-protection (RASP). These solutions help ensure that Android apps remain secure even after launch.

Unprotected mobile applications can be reverse-engineered and exploited in multiple ways.
Tampering and misuse could result in the following security threats; unauthorized access, malicious code injections, credential theft, app cloning, IP theft, broader system attacks, and more.
The best approach to defending your applications is to layer both static and dynamic application protection. Combining code hardening techniques such as code obfuscation and encryption with runtime application self protection (RASP) can help you enhance mobile app protection and remain compliant with the latest regulations.
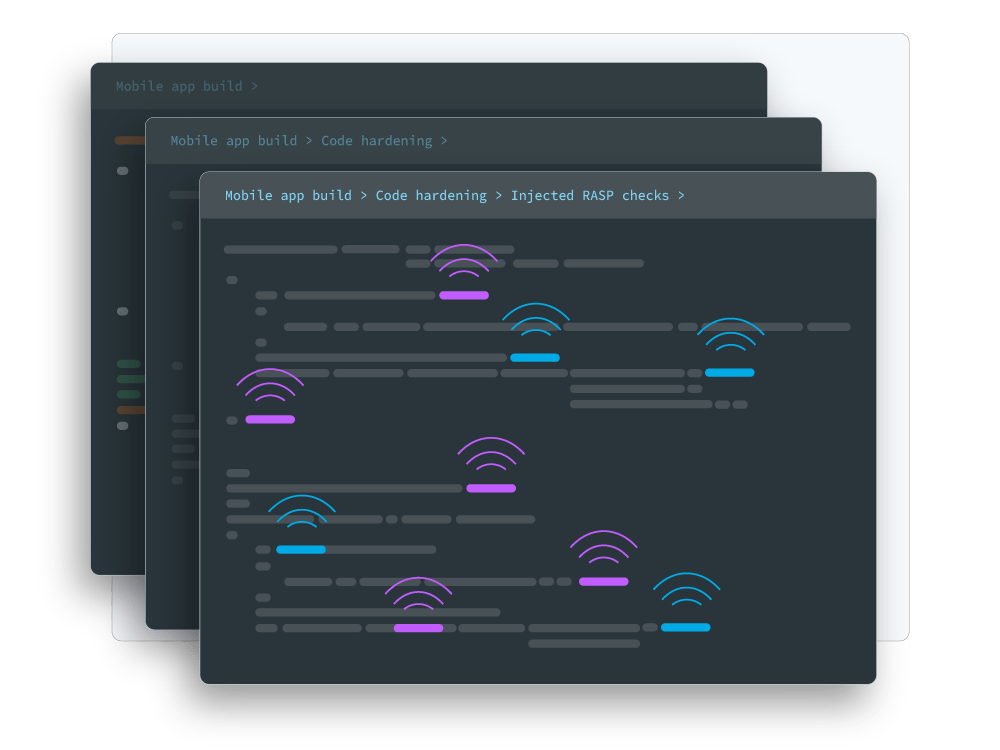
Guardsquare integrates multiple layers of security into the code of your mobile app, protecting against both static and dynamic analysis and runtime threats.
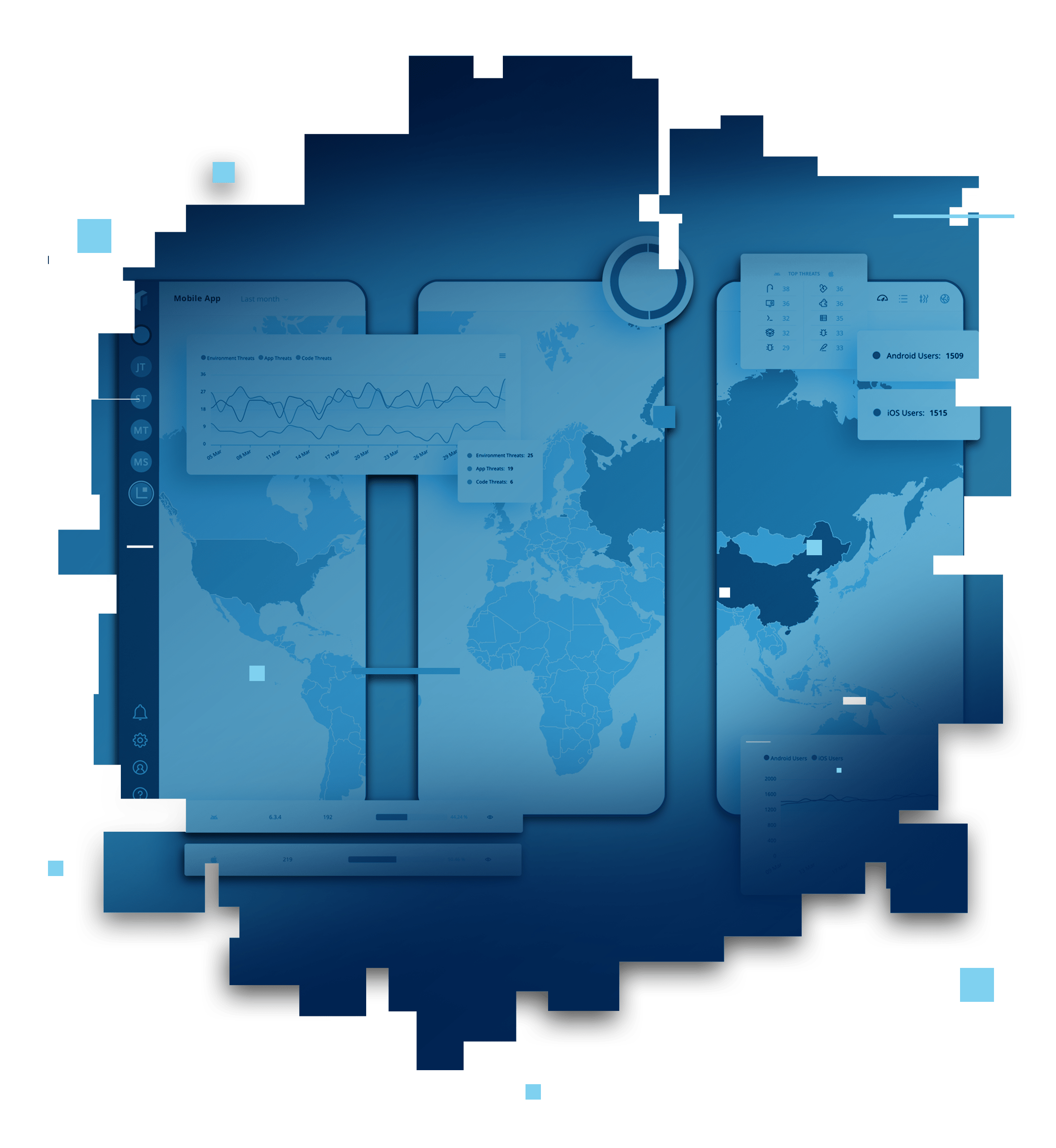
After an Android or iOS app is released, security teams and developers often lack visibility into the most common attack vectors and most targeted parts of their code. Real-time threat monitoring enables teams to identify threats, adapt their security configurations, and protect apps from suspicious activity and malicious users. Android application protection is secured by Guardsquare’s DexGuard solution with code hardening, malware defense, RASP, and more. iOS application protection is secured with iXGuard, Guardsquare’s most comprehensive security solution, using code hardening, RASP, and more.
Guardsquare helps teams implement app security with tools that simplify testing and security improvements at various points throughout the development lifecycle. With its unique combination of testing, code hardening, runtime application-self protection, and threat monitoring, teams using Guardsquare can continuously integrate security.
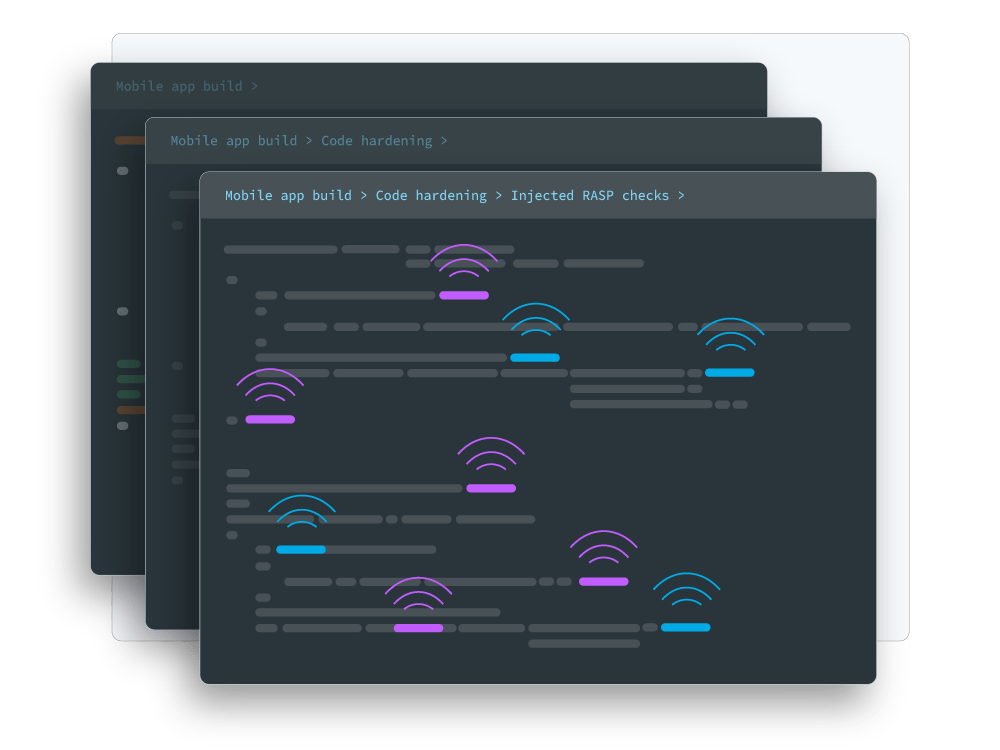
Guardsquare integrates multiple layers of security into the code of your mobile app, protecting against both static and dynamic analysis and runtime threats.
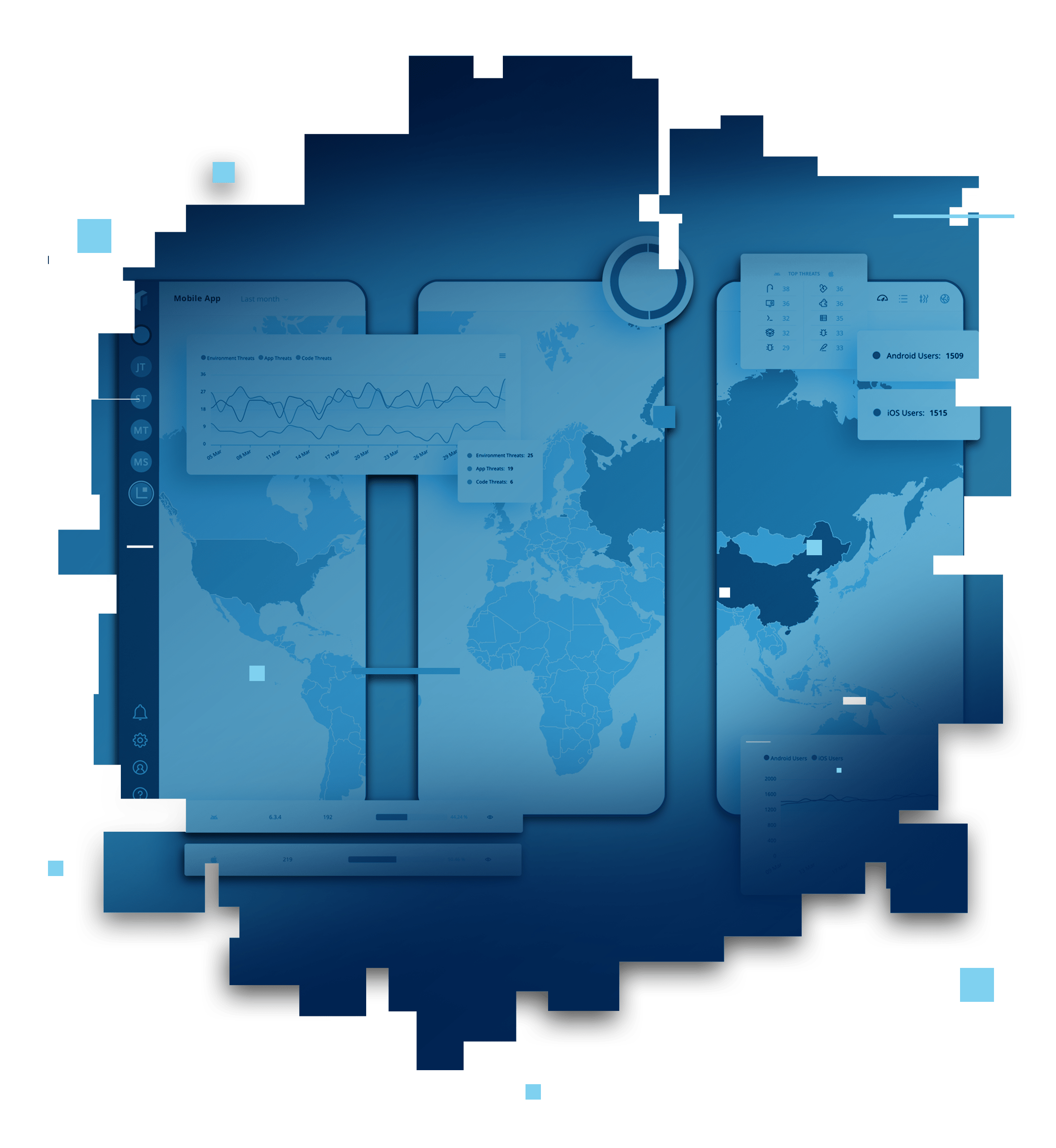
After an Android or iOS app is released, security teams and developers often lack visibility into the most common attack vectors and most targeted parts of their code. Real-time threat monitoring enables teams to identify threats, adapt their security configurations, and protect apps from suspicious activity and malicious users. Android application protection is secured by Guardsquare’s DexGuard solution with code hardening, malware defense, RASP, and more. iOS application protection is secured with iXGuard, Guardsquare’s most comprehensive security solution, using code hardening, RASP, and more.
Guardsquare helps teams implement app security with tools that simplify testing and security improvements at various points throughout the development lifecycle. With its unique combination of testing, code hardening, runtime application-self protection, and threat monitoring, teams using Guardsquare can continuously integrate security.