Better Mobile App Security with Standards: OWASP MASVS 2.0 Automated

Guardsquare supports OWASP
The OWASP (Open Worldwide Application Security Project) MASVS (Mobile Application Security Verification Standard) is a valuable resource for mobile app developers looking to improve the security posture of their iOS and Android applications. The standard is based on the collective knowledge of security experts from around the world and provides both a baseline and a benchmark for security requirements for a mobile application. The model is divided into three layers: standard security (MASVS-L1), defense-in-depth (MASVS-L2), and resiliency against reverse engineering and tampering (MASVS-R).
Since 2021 OWASP has been refactoring its security standard for mobile applications. The objectives are to become more mobile-focused by eliminating overlaps with other OWASP standards, simplifying the scope of some checks that are overly broad, removing checks that can't be verified from an external perspective (e.g. with a security scan or a pentest), and getting rid of redundant checks. The process is open-source and relies on contributors, with discussions on the OWASP Slack channel turning into issues on Github and eventually into a refactored version.
The release of the MASVS 2.0 adds clarity and precision while leaving room for more flexible testing in the MASTG (Mobile Application Security Testing Guide). Guardsquare, a supporter of OWASP's mission, has been contributing to the project while also updating our free, developer-oriented mobile application security testing tool, AppSweep, to support the refactored standard.
How AppSweep by Guardsquare aligns with OWASP Mobile App Security Standards
The refactored OWASP MASVS categories
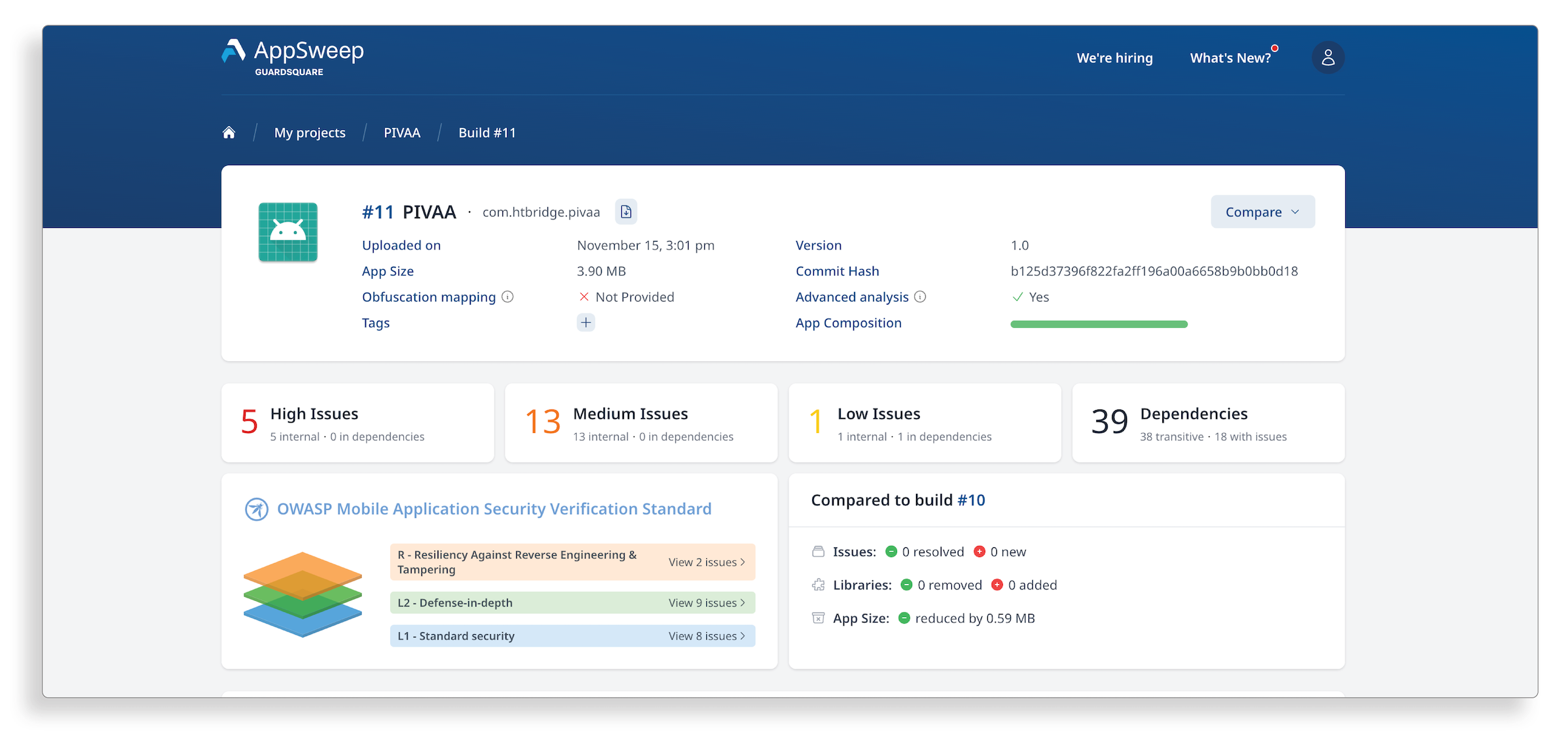
Last April we announced built-in support for OWASP in AppSweep: AppSweep users benefit from additional findings that provide coverage for the OWASP MASTG security requirements. We also added a filterable view of the results to make it easier for users to identify how the findings we report relate to the OWASP MASVS categories.
Recently we’ve introduced additional capabilities that increase our coverage in support of the OWASP MASVS refactor. By enabling users to efficiently understand the vulnerabilities associated with OWASP MASVS categories, developers and security professionals benefit from a targeted, at-a-glance analysis and gain confidence in embedding security best practices in their mobile apps.
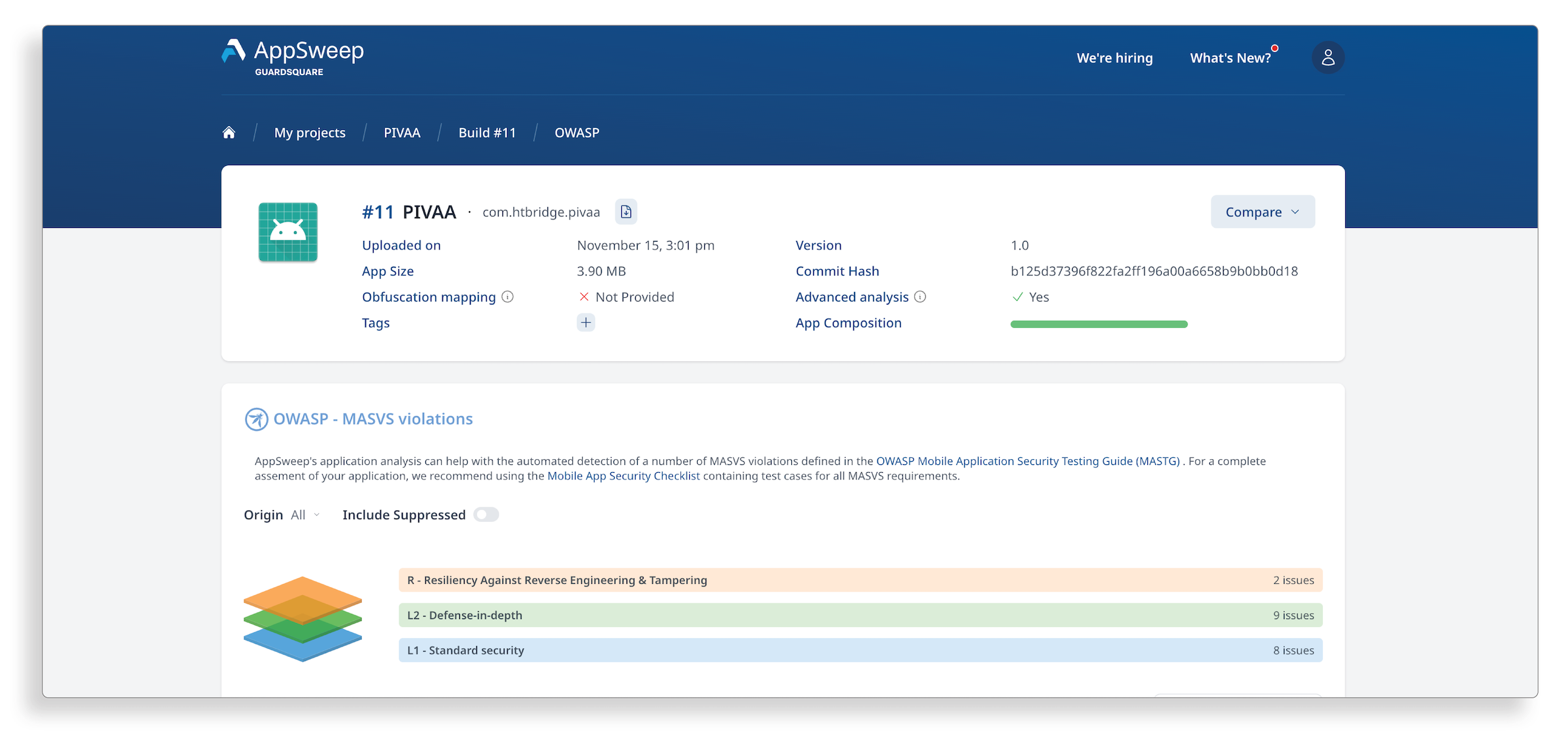 In addition to the categories, AppSweep users can also quickly evaluate their findings along the OWASP MASVS levels. These levels (Level 1, Level 2 or Resilience) are designed to guide you in assessing the security requirements for your app that most closely match your threat model.
In addition to the categories, AppSweep users can also quickly evaluate their findings along the OWASP MASVS levels. These levels (Level 1, Level 2 or Resilience) are designed to guide you in assessing the security requirements for your app that most closely match your threat model.
The concept of security verification levels was initially introduced in the MASVS as an attempt to standardize security requirements to fit different threat scenarios: L1 is the broader baseline for mobile app security, in general. L2 includes defense in depth and additional measures for apps that deal with highly sensitive data. The last level, called Resilience, caters to protection against client-side threats by setting reverse engineering resiliency requirements.
As part of the MASVS refactoring, levels are tied more closely to the set of tests embedded in the MASTG. The rationale behind is that the same control can lead to different tests, depending on the level (or profile) of security that the app needs. That is to say, different tests can be applied based on the required security profile. For example, for MASVS category “Storage”, MASTG Storage-1 and 2 can be required for a health or a financial app that deals with highly sensitive data and needs to fulfill the L2 level, whereas a different app might require to fulfill only L1.
As part of our commitment to OWASP, we will continue to update AppSweep as the MASVS and MASTG change.
Automating checks for optimal visibility into OWASP MASVS compliance
The OWASP MASTG details specific test cases to prove compliance with the MASVS categories. A key benefit of adopting AppSweep is that the MASTG requirements are built into the tool and automated scanning against them can be integrated into the most common CI/CD pipelines (e.g. Jenkins, Github or Bitrise). Running automated checks to assess your compliance with the MASVS enables teams to get continuous feedback on their security efforts.
Incorporating testing as a standard part of your development process ensures vulnerabilities are detected quickly, and can be addressed in a timely and efficient manner by the development team. Delaying it to the final stages of the release process runs the risk of missing issues or having to make tradeoff decisions between meeting schedule pressures or addressing all vulnerabilities. Automating the testing enables the analysis with little to no additional load on the developers. Leveraging the OWASP standards to develop threat models and vulnerability testing is a best practice, especially for mobile apps that are required to meet industry compliance requirements.
Staying ahead in the rapidly changing mobile app security landscape
With development teams typically being understaffed and overcommitted, it is a challenge for them to develop the functionality needed and stay up-to-date on a constantly evolving security landscape. Standards like OWASP MASVS enable development teams to adopt a security framework for their application and leverage the collective expertise of the wider community of security researchers.
Efforts such as the refactored MASVS v2 are a great example of capturing growing experience and expertise of the community. Our AppSweep development team is committed to ensuring the product evolves to support the relevant elements of the new standards.




