ThreatCast Mobile App Security Console Adds More Intelligence to Help Teams Stop Attacks

Updated June 16th, 2025
In 2020, we launched our mobile app security console, ThreatCast, to provide visibility for DexGuard and iXGuard customers into what happens to their mobile apps after they are published and downloaded. A previous blog highlighted the kinds of insights ThreatCast enables teams to access. With recent updates to the latest versions of DexGuard and iXGuard, ThreatCast users can now gain even more insight out of the data—and take action.
Since its launch, ThreatCast has enabled teams to see:
- What types of attacks apps are facing
- How they were discovered
- How long it takes an attacker to perform a certain type of attack after a new app release.
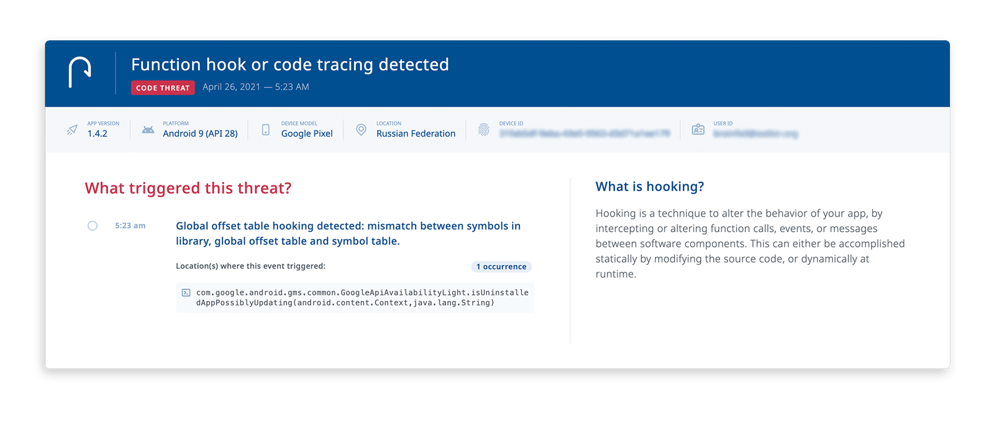
Now, when using the latest DexGuard and iXGuard versions, teams can also decipher where in the code the attack happens, and who attacked it.
Three actionable insights with this additional info
This update provides teams with three key insights that help them take action and better protect their mobile apps.
1. Granular security configuration insights for future releases
Within DexGuard and iXGuard configurations, teams can already specify, for each RASP detection type, how aggressive the injected security checks will be. They can also build a response strategy based on certain detected threats.Now, with the additional knowledge of which classes and methods of the app have been attacked, teams can further optimize RASP integrity checks for future builds. In other words, they can become more aggressive with protections in “frequently attacked” parts of the code. Teams can also evaluate and fine-tune their response strategies for dedicated threat types based on observed attack vectors.
2. Reveal ThreatCast data to your support team
Now, the configurable “user identifier” feature will allow teams to link data from ThreatCast to any other session data stored in backend systems. This allows teams to identify malicious actors. In practice, this means that your support team can determine when they receive complaints about crashing on non-functional apps whether this is due to an attack or compromise.
Teams can use this information to decide whether to further investigate the support request or not, saving them time and avoiding accidentally aiding attackers. For example, sometimes when a crash happens it is due to a bug in the software that needs to be addressed. Other times it is because a user (possibly a malicious user) is using a jailbroken device. Now, ThreatCast users can quickly understand whether a jailbroken device is being used, leading to faster response time and less time spent helping users who are breaking the rules.
3. Integrate with your team’s favorite tools to simplify workflows
With any paid ThreatCast subscription, teams can integrate security insights into their favorite tools. By making use of the new webhook integration feature, teams can have specific threat events forwarded to any selected destination.
Real-time ThreatCast feeds can be integrated into anti-fraud systems, helping teams quickly identify which user is causing a specific threat. Teams can collect relevant security intelligence and determine what action to take based on observed threats and patterns. For example, teams can block a transaction or suspend a user or device from the app. This is a powerful and efficient way to prevent further damage to the app, revenue streams, and brand reputation.
The same webhook integrations allow for seamless integration with your SIEM, so you can have all of your security information in one place. Additionally, teams can integrate ThreatCast webhook payloads with CRMs and customer support portals, as well as any other backend system.
Get started today
ThreatCast started out as a powerful mobile threat console for gaining insights into attack vectors for mobile apps after they are released into the wild. Now, with the increased insight available in the new versions and with a Premium ThreatCast subscription, teams can quickly and efficiently take action based on security intelligence.
To start using these new features, upgrade to the latest versions of DexGuard for Android and iXGuard for iOS. Premium subscribers get access to additional, vital intelligence to help them better protect their entire app suite.




