How Guardsquare Helps Apps Comply with PCI Mobile Payment Acceptance Security Guidelines

The popularization of online payments has unquestionably revolutionized banking, commerce and retail. The convenience it has brought merchants and consumers however, has also notably provided hackers with yet another gateway for cybercrime. Guardsquare provides security solutions that safeguard mobile apps against reverse engineering and hacking. Our solutions enable a trusted execution environment for processing electronic payments on mobile devices and comply with a number of guidelines introduced by the PCI Security Standards Council (PCI SSC).
In light of the recent compliance discussions, and regulatory updates issued by the PCI SSC to foster the safety of mobile payment transactions worldwide, we will be presenting a short blog series discussing how PCI regulations apply to mobile.
In the next two blogs, we will discuss two important standards applicable to the mobile ecosystem: the PCI Mobile Payment Acceptance Security Guidelines and PCI SPoC. This week we begin by focusing on how our software solutions DexGuard and iXGuard can help app developers implement the PCI Mobile Payment Acceptance Security Guidelines.
Mobile payment apps and PCI compliance
Being PCI compliant at the app level means ensuring all user credit card information is securely processed via mobile apps by, for example, using encryption, ongoing monitoring, etc.
Overall, mobile app PCI compliance means your application meets an accepted industry standard for handling users’ credit card information. This standard is achieved through meeting a series of objectives and guidelines for the security of payment transactions, as well as for the risk and controls in the supporting environment, provided in the PCI Mobile Payment Acceptance Security Guidelines for Developers.
How Guardsquare can help
Guardsquare provides security solutions that clients can use to help with mobile app PCI compliance. Our mobile protection software, DexGuard (Android) and iXGuard (iOS), provide features such as obfuscation, RASP, tampering prevention, etc. to meet some of these security requirements. For example, obfuscation is relevant in protecting the code that handles and stores credit card information, RASP is applicable in securing the devices on which credit card transactions are done.
Securing your financial transactions at the app level is key in protecting your customer data against unauthorized access. Guardsquare provides solutions that meet a series of PCI SSC technical guidelines for apps accepting electronic payments on mobile devices, in section 4 of the PCI Mobile Payment Acceptance Security Guidelines for Developers, as explained below:
4.1 Prevent unauthorized logical device access.
Guardsquare meets compliance of this requirement by applying code obfuscation to hide sensitive APIs and mangle critical operations in the app. This is complemented by our runtime protection suite that detects application tampering, device rooting, application debugging, function hooking, code injection, etc.
4.2 Create server-side controls and report unauthorized access.
DexGuard's device fingerprinting option allows the mobile application to uniquely identify the user’s mobile device to the backend server and any monitoring systems in order to report unauthorized access.
4.3 Prevention of escalation of privileges.
DexGuard and iXGuard platform integrity checks, as discussed above, detect compromised devices and dynamic attacks. These integrity checks are crucial to preventing the risk of privilege escalation.
4.7 Harden the applications.
Our Android and iOS tamper detection checks are able to verify the integrity of the application signature upon launching the app, in addition to detecting other forms of tampering such as code injection and repackaging. This is, once again, complemented by our runtime protection suite and network hardening capabilities, such as SSL Pinning.
4.9 Conform to secure coding, engineering, and testing.
Notably, this guideline references the Mobile OWASP top 10, that identifies threats "M8 - Code Tampering" and "M9 -Reverse engineering", and recommends runtime application self-protection and obfuscation as countermeasures.
4.11 Protect the mobile device from unauthorized applications.
An authorized mobile app must have some mechanism that permits authentication of the source and integrity of the executable file. Our tamper detection checks are able to verify and protect the integrity of the application in order to prevent any unauthorized modifications.
4.13 Protect the mobile device from unauthorized attachments.
Guardsquare meets this requirement with DexGuard, by providing Android apps with the best integrity assurance through the mutual authentication between the entry device and the mobile device via device fingerprinting.
4.16 Provide an indication of secure state.
A secure state of the application is often guaranteed when it runs in a trusted execution environment. Such a secure environment must indicate to the user that the app is executing in an uncompromised state, which is possible through implementing DexGuard and iXGuard runtime protection features.
Conclusion
As mobile applications play an increasingly central role in payments, app security and compliance become imperative for all stakeholders involved. Our security software help ensure the overall effectiveness of your IT security architecture by safeguarding your mobile endpoint. Ensuring app and platform integrity, through preventing reverse engineering and hacking, is also key in meeting multiple security points listed in PCI.
In short, our technical solutions fulfill specific PCI mobile app payment guidelines, such as obfuscation of critical code and resources used for unique identification, to prevent replication and misuse of that information; Software and platform integrity testing, to ensure a trusted/secure execution environment; SSL pinning, to protect communications to the backend from eavesdropping or interception.
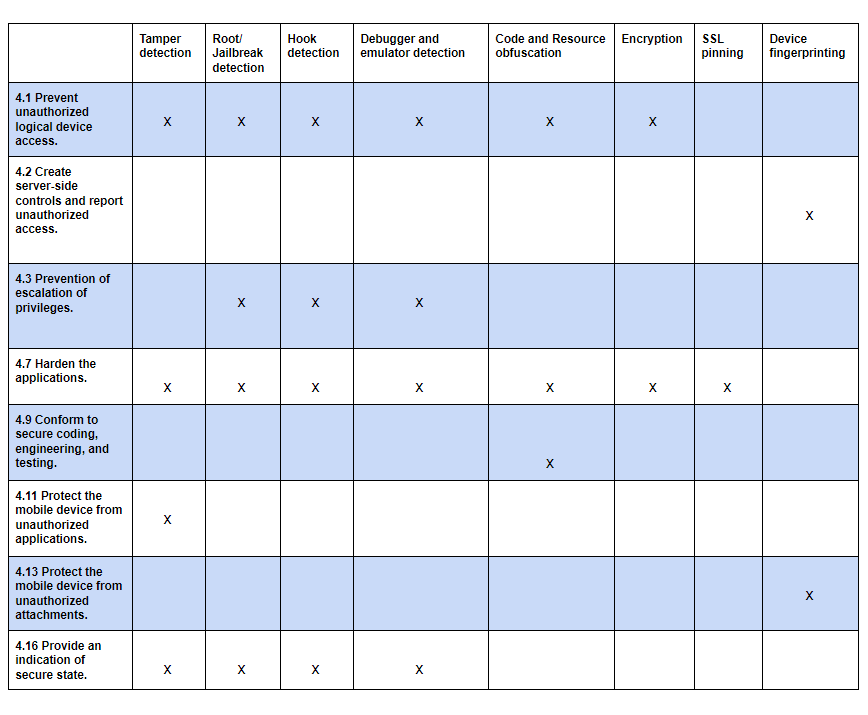
As the global reference in mobile app protection, Guardsquare help clients meet a series of PCI SSC guidelines for applications accepting electronic payments on mobile devices, as summarized in the following table: