How to Protect Your App From iOS Piracy
Global app revenue reached $120 billion in 2020 and a growing percentage of that revenue is generated by in-app spending. As much as 96% of consumer spend in non-gaming apps is generated by in-app subscriptions. This vital in-app revenue is endangered by piracy, both through the distribution of modified or “cracked’ apps, on both Android and iOS, and through the use of so-called “tweaks”, scripts that modify the behaviour of mainly iOS apps. Both forms of piracy enable users to access premium content and functionality for free, impacting the revenue stream of many organizations.
To illustrate the magnitude of the problem, our team searched the internet for tweaks for popular iOS apps. We focused on iOS as the vulnerability of iOS apps to reverse engineering and piracy is the most underestimated. It took us less than half a day to find more than two hundred tweaks in different repositories. We analyzed the found tweaks to better understand how they work and how app developers can protect iOS apps against the resulting revenue loss.
What you need to know about “tweaks” through piracy on iOS
Tweaks for iOS apps can freely be downloaded from third party app stores. The only two things users need to install and use them is a jailbroken device and a graphical user interface like Cydia, Sileo or Zebra to integrate the tweaks in the targeted application. The installation process is very similar to installing an app from the App Store, meaning that it doesn’t require any specialized skills or knowledge from the user. Once installed, the tweaks use a technique called hooking to modify the intended behaviour of the application while it is running. In most cases, the tweaks bypass the license or purchasing checking mechanisms of the targeted applications to give the user access to paid content or functionality. Other tweaks for iOS piracy are designed to remove ads and/or branding from applications or to disable security checks meant to prevent apps from running on jailbroken devices (jailbreak detection).
What we found
The 200+ tweaks we analyzed target applications in all App Store categories. A large part of the “tweaked” apps we found belong to the category of photo and video applications, but we also encountered tweaks for finance, shopping, gaming, and other applications.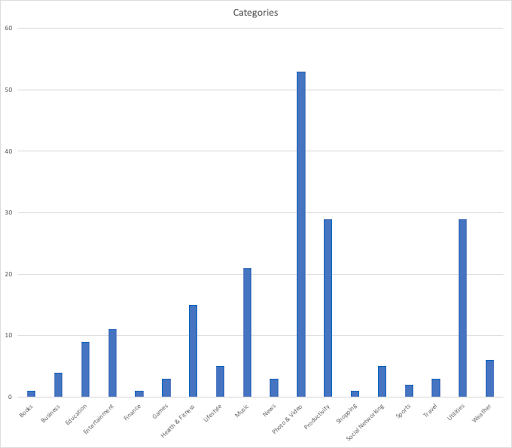
Analyzed tweaks per App Store category
Analyzed tweaks per App Store category
Remarkably, it is not only apps belonging to small companies that fall victim to piracy on iOS apps through tweaks. A large share of the found tweaks target applications developed by large corporations and with presumably hundreds of thousands - if not millions - of users. This illustrates how widespread an issue iOS app tweaking is and how few organizations are taking sufficient mobile app security precautions. The following graph gives an idea of the popularity of the impacted applications using the number of available reviews for each included app as a proxy for popularity.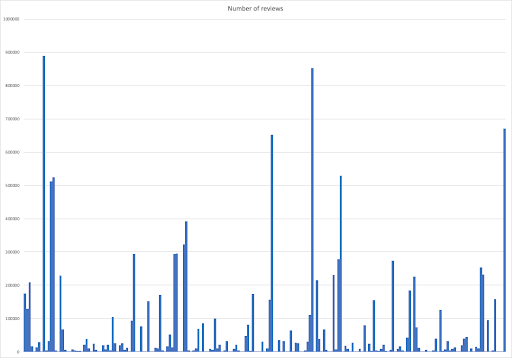
Number of reviews in the US App Store of all the targeted apps in our research
Number of reviews in the US App Store of all the targeted apps in our research
As far as functionality goes, 93% of the analyzed tweaks were designed to provide free access to premium features or content to users; a significant share of these tweaks also removed jailbreak detection mechanism to make this possible. The unlocked features vary greatly as they depend on the type and category of the target application. Here are a few examples: one of the included tweaks unlocks advanced photo editing settings and functionality and gives users access to additional filters and themes in a leading photo editing application. Another tweak enables users to access all premium functionality for free in a popular utility app, undermining the freemium business model adopted by the app publisher. The remaining tweaks in our batch were built to disable built-in jailbreak detection mechanisms or to remove ads/branding from the targeted iOS applications.
What is at stake
The use of app tweaks can have a significant impact on the revenue generated by the affected applications and on the overall company revenue of the app publishers. To illustrate what is at stake, we looked at the losses tweaks can cause for 20 common apps belonging to some of the categories most frequently targeted by this kind of piracy (photo and video editing applications, note taking applications, document readers, VPNs, media streamers, password managers etc.). For these 20 applications, the lost revenue ranged from $1.25 to $14.99 per user per month depending on the unlocked functionality, with an average of $8.31 per user per month. These small monthly losses can have an important impact on overall revenue. We did the math for the leading photo editing application mentioned above. Based on the assumptions that 0,4% of the iOS devices are jailbroken and that 1 out of 10 app users write a review, the losses in revenue for the app amount to $ 207,152 per month or $ 2,485,824 annually.
How To Protect Your iOS App
During our research, we found that app developers try to prevent piracy through two different approaches - both of which, based on our research findings, are clearly not as effective as they need to be. The first iOS piracy defense is to multiply the number of purchase/license checks performed by the application. Without solid code obfuscation in place, these checks can easily be identified and neutralized. We have found tweaks that hooked up to 89 different methods across the source code to bypass all the purchase/license checks. The second approach consists of implementing mostly DIY jailbreak detection checks to prevent the apps from running on a jailbroken device. 18% of the targeted applications in our research have some kind of jailbreak detection built in. Without additional application shielding measures in place, this security measure is insufficient as the checks are easy to circumvent. In fact, a significant amount of the tweaks we analyzed hook jailbreak checks as part of the process of unlocking premium functionality. Users can also install tweaks specifically designed to bypass jailbreak detection mechanisms.
The most effective way to protect iOS applications against piracy is to adopt a multi-layered approach to app protection combining advanced environment integrity checks, including jailbreak detection, with code integrity checks that prevent the app from being modified at runtime (hook detection, tamper detection) and code obfuscation. iXGuard, our security solution for iOS apps (and DexGuard for Android apps), provides multilayered app protection without affecting end-user experience.




