DexGuard provides much more advanced functionality than ProGuard. The good news is that it is easy to upgrade the protection of your Android applications. You won't have to hire expensive consultants to get the software to work, you won't even have to reconfigure your build system. You can start from your existing ProGuard configuration and implement DexGuard's additional layers of protection in a series of consecutive steps.
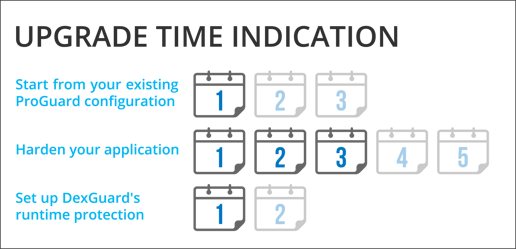
1) Start from your existing ProGuard configuration
DexGuard is backward compatible with ProGuard. You can re-use your existing ProGuard configuration file and get started with DexGuard. Since DexGuard processes all the components of your Android application (and not just the bytecode), you will have to add some keep rules to correctly preserve the libraries, resources, resource files and assets that are used by reflection. The actual time needed to configure DexGuard depends on the amount of reflection in your code and can vary from a couple of hours to three days at the most.
2) Harden your application
At this point, DexGuard will only provide basic obfuscation (name obfuscation). To make use of DexGuard’s advanced code hardening capabilities, you will have to identify the components (classes, strings, assets etc.) of your application that need additional protection and obfuscate or encrypt them with a few configuration options. Successful implementation requires some trial and error. Small projects can be configured in three days or less; projects with many external libraries can take up to five days to configure.
3) Set up DexGuard's runtime protection
DexGuard integrates various runtime self-protection mechanisms into your Android application to protect it from dynamic analysis and live attacks. To make use of DexGuard's runtime protection, you need to implement a few simple API calls from your application. Do not forget to harden these calls with DexGuard’s static protection. Setting up the runtime protection mechanisms takes one to two days.
Support available!
- DexGuard comes with a tuned configuration for the Android Runtime.
- DexGuard performs automatic instrumentation of code at runtime to account for some amount of reflection. This will help you to set up DexGuard more efficiently.
- The DexGuard documentation outlines a series of best practices to help you protect your Android application.
- DexGuard comes with working sample projects demonstrating its capabilities.
- Our security engineers are available to help you solve any technical issue you may encounter.