The Role of Mobile App Security in FDA Approved mHealth Apps

This blog explores:
- The mHealth app market is growing, but FDA approval and a rise in security threats makes a strong security posture essential.
- Following the FDA’s STRIDE framework is a great place to start when seeking FDA approval and building a robust security strategy.
- Guardsquare’s DexGuard, iXGuard, AppSweep, and ThreatCast products can help you meet and maintain FDA approval and properly secure your mHealth app.
Whether you have taken cardiac measurements, measured or sent blood-glucose information, or accessed medical diagnostic records from a mobile device, you’ve most likely interacted with a mHealth app (also referred to as a mobile medical app). With mobile medical app offerings increasing, many healthcare organizations, medical device manufacturers, and independent healthcare professionals are considering bringing their own apps to market.
While we always recommend an app development team consider security as an important part of the development process, FDA approval adds another layer of complexity to certain mHealth apps.
In this post, we’ll explore the critical role of mobile app security in obtaining FDA approval for mobile medical apps, ways to pursue mobile app security for the initial approval process, and how to continue to keep security top of mind after the app goes live to maintain FDA approval.
mHealth apps: The rising star of healthcare technology
In the next five years, the mobile app health market is estimated to have a year-over-year growth of 17-18%. Much of what drives this growth is convenience. According to Mobius MD, 43% of millennials prefer to access patient portals from their phone. They have a variety to choose from. The Android app market alone boasts more than 325,000 mHealth apps.
So what exactly qualifies as a mobile medical app, and what does the FDA have to do with them? The FDA defines a mHealth app as any mobile technology that allows the user to monitor and share health information, including apps that allow physicians to diagnose and deliver care.
With that, it’s easy to see the relevance of FDA influence in app approval. In fact, the FDA is responsible for ensuring the safety, efficacy, and security of medical devices, which includes (you guessed it!) mobile medical apps.
Understanding FDA Approval for mHealth Apps
In some mHealth apps, you may be accessing information that helps you track or self-manage a condition or disease, like Fooducate, an app with over 300,000 nutrition profiles preprogrammed to help users identify healthy foods and keep their blood sugar levels in the recommended ranges. Or, you may use an app provided by your healthcare group to access your personal health records (PHRs). While these apps may hold sensitive information, they are considered minimal risk and are NOT subject to FDA approval.
FDA approved mHealth apps typically include those that transform a mobile platform into a regulated medical device. For instance, apps that serve as accessories to regulated medical devices or those that function independently as medical devices are subject to FDA approval. An example would be AliveCor, an app that includes an attachment that turns the user’s smartphone into an electrocardiogram. This could also look like an app that serves as an accessory to a regulated medical device — like NeuroMetrix, an app that adjusts the functions and settings on their wearable pain relief devices. Both of these examples require strong security measures to ensure the information provided, collected and transmitted by the user's app, as well as the medical research or technology embedded inside the app, is safe.
Still unsure of whether your mHealth app requires FDA approval? You can use the decision tree below and visit the FDA’s Digital Health Regulatory Policies page to help you determine if your app requires FDA approval:
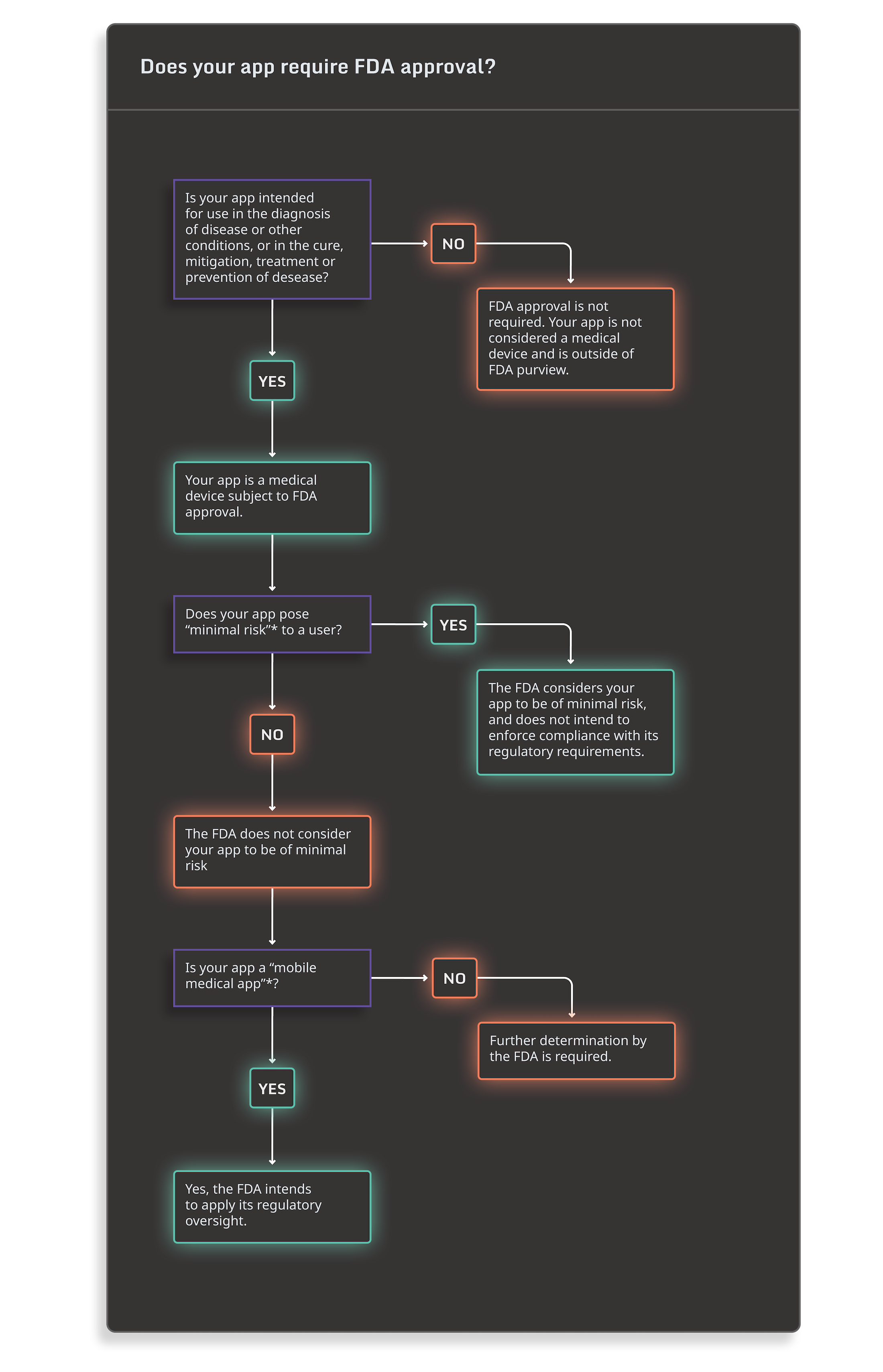
*As defined by FDA’s Policy for Device Software Functions and Mobile Medical Applications.
What do FDA approved mHealth Apps Have in Common?
Secure mHealth apps share common features and practices aimed at safeguarding sensitive health information, maintaining user privacy, and ensuring the overall security of the application.
Once you determine your mHealth app qualifies as a medical device and requires FDA approval, it’s time to integrate robust software security measures. This is integral for compliance and to ensure the safety and efficacy of FDA approved mHealth apps.
In its example risk playbook, the FDA recommends using the STRIDE framework as a guide to help navigate the approval process of a mHealth app. The app in question should implement measures to mitigate:
- S - Spoofing
- T - Tampering
- R - Repudiation
- I - Information Disclosure
- D - Denial of Service
- E - Elevation of Privileges
This STRIDE framework allows you to ensure the efficacy, safety, and security of your apps, which smooths out the FDA approval process. The lengthy FDA approval process can take months to years. For FDA approved mHealth apps, safeguarding patient health and data is paramount. Developers must proactively address security vulnerabilities to prevent potential exploitation.
For FDA approved apps, particularly those in the mHealth sector, inadequate security can lead to compromised patient data (e.g., PII/PHI), potential recalls, substantial fines, civil lawsuits, and significant damage to the organization's reputation and trust.
Let’s explore two examples of what this can look like for an organization in the real world.
Application recalls
In 2017, researchers found some disturbing vulnerabilities in widely used insulin pumps. They found that unencrypted communication between the pumps and their remote controls allowed them to use reverse engineering to understand the program’s signal communication and bypass validity checks.
What does this mean? With knowledge of the program’s signal communication an attacker could remotely target these pumps and be able to withhold insulin or trigger a potentially lethal dose. The researchers demonstrated the danger of the app to FDA officials, and the organization behind the insulin pumps and regulatory apps announced a voluntary recall program a week later.
While this recall situation doesn’t specifically involve a mhealth app-connected medical device, it’s easy to see how a similar vulnerability could be exploited in mHealth apps. These types of recalls are not only costly to the app’s creators, but can cause irreparable damage to the organization's professional reputation.
Financial loss and FDA penalties
According to the U.S. government and TechTarget, healthcare cybersecurity breaches are on the rise. In just the first five months of 2022, the number of healthcare breaches was nearly twice that of last year’s figures from the same time period.
While experts believe a variety of factors contribute to the cause of this dramatic increase, the effects of these breaches are straightforward. Early in 2022, Inmediata Health Group reached a $1.13M settlement stemming from a data breach in 2019 that affected nearly 1.6M patients.
While this breach was due to a misconfigured website and not the provider’s mobile app, the increasing preference for end customers to use mobile platforms creates another channel for threat actors to exploit. Unprotected mobile apps, running on a private mobile phone, outside the control of the provider, create ideal opportunities for threat actors to target the sensitive information typically accessed by mHealth applications.
In addition to the threat of a class action suit, The FDA can (and will) take action against regulated mHealth apps that do not comply with their security standards.
These risks and the potential financial, reputational, and civil fallout that can occur as a result of a mHealth app breach emphasizes that security for your mHealth app should be paramount.
Getting started with mobile app security for your mHealth app
Mobile application protection can be daunting, from ensuring your app is protected against reverse engineering and tampering, to implementing proper security protocols to meet FDA approval requirements. But it doesn't have to be.
By incorporating AppSweep, our free automated app scanning tool, into your CI/CD toolbox, you can easily and accurately improve your app’s security during the development cycle. Made for developers, AppSweep, can help you identify and fix security issues as well as dependencies by providing practical recommendations and insights for you and your team. Additionally, AppSweep has built-in support for OWASP MASVS Categories, providing more high-quality actionable insights.
Guardsquare's mobile application protection solutions, DexGuard and iXGuard, provide comprehensive mobile application security with easy integration. Guardsquare’s polymorphic approach ensures that every app’s build comes with a unique combination of check locations and exact checks, ensuring threat actors cannot use any prior code knowledge they may have in their effort to reverse engineer an app.
Similarly, ThreatCast provides real-time visibility into threats after the app is released to help you proactively analyze threat actors’ attempts at tampering. ThreatCast gives your team the much-needed insights it needs to continuously improve your app’s security posture, in line with the FDA’s security recommendations.
By leveraging Guardsquare’s multi-layered approach to testing, protecting, and monitoring your mHealth apps, you can confidently protect them against Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privileges – the core risk categories in the FDA’s STRIDE framework. Ensuring that your app is protected against all STRIDE threats can help you achieve and maintain FDA and non-US regulation approval (e.g. EU MDR). In other words, these regulating bodies see robust security protocols as a commitment to protect and maintain your apps’ and patients’ security.
Learn more about how Guardsquare can help you obtain FDA approval for your mHealth app.





